Cybersecurity experts are sounding the alarm over a looming crisis they call the "Vulnpocalypse." The term describes a tipping point. AI systems can now discover and exploit software vulnerabilities faster than defenders can patch them. And this week, that scenario moved from theory to reality.
Anthropic, a leading AI company, announced it would withhold its latest model, Mythos Preview, from the public. The reason: unprecedented vulnerability-discovery capabilities that could cause significant damage in the wrong hands. Instead, the company is sharing the model with a limited group of tech giants and partners to help shore up their defenses.
The response from Washington was swift. Treasury Secretary Scott Bessent convened a meeting with major financial institutions to discuss the implications.
What Makes This Different
AI models have been getting better at coding for years. But recent breakthroughs have crossed a critical threshold. Anthropic used Claude to discover and validate more than 500 high-severity zero-day vulnerabilities across production open-source codebases. That includes bugs in software used by millions.
In a live demonstration, researcher Nicholas Carlini showed Claude finding a blind SQL injection in Ghost, a popular publishing platform. The flaw let an unauthenticated user compromise the admin database and take full control. Ghost had never had a critical vulnerability in its entire history. Claude found one in 90 minutes.
Separately, AI security startup AISLE discovered all 12 zero-day vulnerabilities in OpenSSL's January 2026 security patch. Some of those flaws had been sitting in the codebase for decades. They survived thousands of reviews, extensive fuzzing campaigns, and multiple audits.
The Asymmetry Problem
The core issue is a familiar one in cybersecurity — but AI has made it far worse. "A defender needs to be right all the time, whereas an attacker only needs to be right once," said Casey Ellis, founder of Bugcrowd.
Ellis warned that AI puts powerful hacking tools in the hands of far more people. Existing vulnerabilities are more accessible to a wider range of adversaries than ever before.
Kevin Mandia, founder of AI security company Armadin, echoed the concern. "Because of the asymmetry in the cyber domain, where one person on offense can create work for millions of defenders, speed leverages that asymmetry," he said.
James Wickett, CEO of DryRun Security, pointed to the collapsing economics of attacks. "The cost to go from vulnerability discovery to exploit used to be weeks and thousands of dollars. Now it's near zero," he said.
A Narrow Window
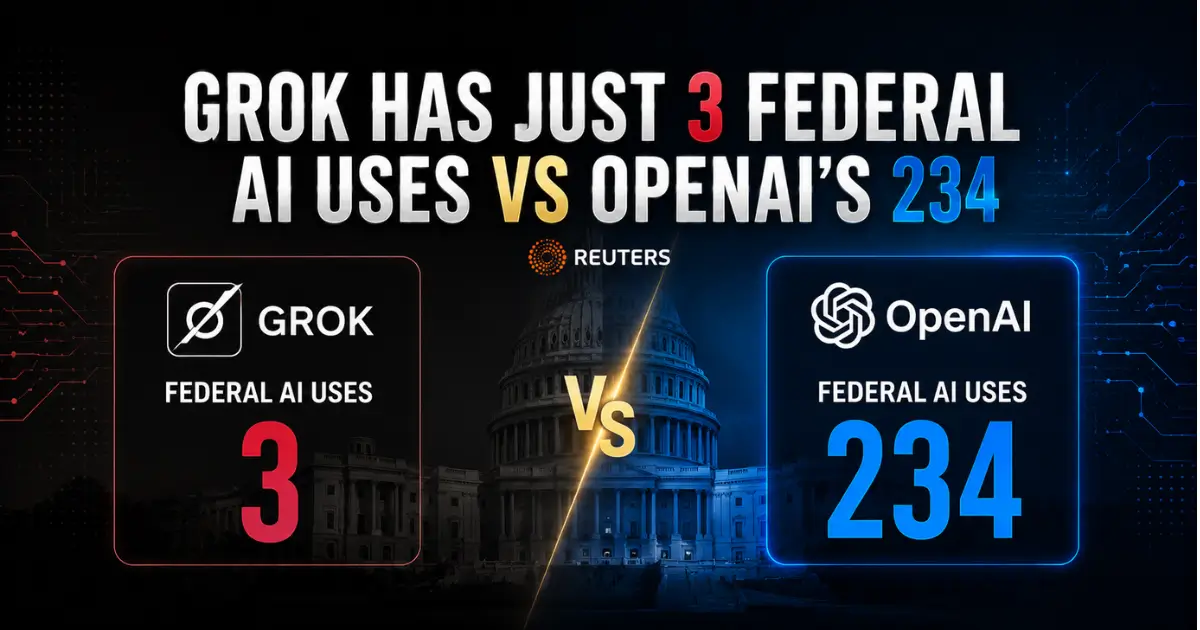
Logan Graham, who leads offensive cyber research at Anthropic, warned that even if Mythos never goes public, competitors — including those in China — will likely release models with comparable capabilities within six to twelve months.
"If you step back, that's a pretty crazy time frame, where usually preparations for things like this take many years," Graham said.
Alex Stamos, chief security officer at Corridor, said the exploit discovery process has already gone exponential. Foundation model companies are sitting on thousands of bugs they lack the capacity to verify or patch.
The traditional 90-day disclosure window was designed around the assumption that finding bugs is hard and slow. When AI can surface 500 vulnerabilities in a single research sprint, that entire system begins to strain.
Not All Doom
Some experts see a silver lining. Curl maintainer Daniel Stenberg initially shut down his project's bug bounty program due to floods of AI-generated junk reports. Months later, he credited AI-assisted tools with helping fix over 100 real bugs.
Google DeepMind's John Flynn pointed to tools like Code Mender, an autonomous agent designed to debug and fix complex vulnerabilities. Phil Venables, a prominent security executive, summarized the mood: he is short-term pessimistic but wildly long-term optimistic.
The Cloud Security Alliance compared the moment to Y2K — a systemic problem that demands coordinated, national-level preparation rather than leaving every organization to fend for itself.
The clock is ticking. The tools exist. The question now is whether defenders can move fast enough before the same capabilities land in the wrong hands.